June 4, 2021
Cloud breaches make exciting headlines, but in most cases, the breach is the user’s failure, not the cloud provider. Gartner predicts that 99% of cloud security failures will be the customer’s fault through 2025.[1]
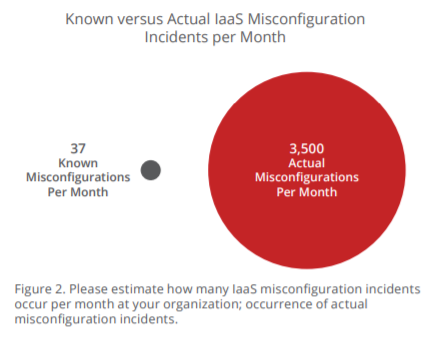
All too often, the weakness exists in cloud policies and implementation—not in the security of the cloud itself. Misconfigured policies, inconsistent architecture, or poor management of cloud services are typically the origin of these breaches. A report from McAfee “found that about 99% of misconfigurations go unnoticed by companies using IaaS.” Enterprise companies told the company that they were aware of, “on average, 37 misconfiguration incidents per month. Yet our real-world data shows that companies actually experience closer to 3,500 such incidents.”[2]
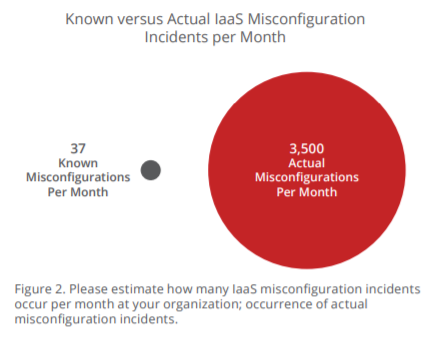
Figure 1: McAfee, Cloud-Native: The Infrastructure-as-a-Service (IaaS) Adoption and Risk Report
Ready For Battle
Complex cyberattacks are on the rise. In the first quarter of 2020, DDoS attacks increased by 242% year over year and by 542% compared to the previous quarter.[3] Cloud Service Providers have the infrastructure, advanced security tools, and expertise to protect your customers by preventing and mitigating cyberattacks.
Security for the Modern Workplace
The cloud is agile and robust enough to remain secure even in challenging scenarios. For example, cloud desktops enable businesses to have employees work from anywhere while maintaining security at an enterprise level. Centralizing desktops in the cloud can reduce the security boundary, making it easier for IT to manage. And keeping operating systems and apps up to date becomes significantly easier with controls centralized by the cloud. Depending upon configuration, cloud desktop solutions can ensure data does not reside on the employee’s device.
Shifting the Compliance and Regulation Burden
Highly regulated industries—such as finance, healthcare, and education—must contend with strict data and security requirements. Securing certifications and compliance is costly and time-consuming for businesses. Selecting a cloud provider that already has all the required compliance and regulatory certificates can be a significant benefit to businesses.
Your Role (and Opportunity)
Delivering everything from backup and recovery to cloud infrastructure solutions, our Stellr team of experts will provide you with the support needed to ensure your customers are secured. Some of these solutions include:
- Cyber & network security
- Cloud security
- Cloud storage & cloud automation
- IaaS/PaaS/SaaS offerings
- Trainings, programs, technical support, & consulting services
Contact us at stellr@synnex.com for help engaging and supporting your customers with their digital transformation & security needs.
[1] Gartner, Is the Cloud Secure? https://www.gartner.com/smarterwithgartner/is-the-cloud-secure/
[2] McAfee, Cloud-Native: The Infrastructure-as-a-Service (IaaS) Adoption and Risk Report https://www.mcafee.com/enterprise/en-us/forms/gated-form.html?docID=be66d487-f531-4484-ba0c-558b534ff779
[3] Nexusguard, DDoS Threat Report 2020 Q1 https://blog.nexusguard.com/threat-report/ddos-threat-report-2020-q1